Description
The Fundamentals of .NET Application Security course lays the foundation required by all application developers and development organizations to produce applications with greater stability and fewer security risks to the consumer.
$9.00 – $9.00 Tax Incl.[break /]
Software defects, bugs, and flaws in the logic of the program are consistently the cause for software vulnerabilities. Analysis by software security professionals has proven that most of the vulnerabilities are due to errors in programming. Hence, it has become a must for organizations to educate their software developers about secure coding practices.
Attackers try to find security vulnerabilities in the applications or servers and then try to use these vulnerabilities to steal secrets, corrupt programs and data, and gain control of computer systems and networks. Secure programming is a defensive measure against attacks targeted towards application systems. This is done throughout the software life cycle that involves designing, implementing, and deployment of applications.
The Fundamentals of .NET Application Security course will be invaluable to software developers and programmers alike to code and develop highly secure applications and web applications. In this First Byte program, you’ll learn how the attackers exploit vulnerabilities in Web and stand-alone .NET applications. You will also learn various techniques and countermeasures to design applications that are resistant to these attacks. Sound programming techniques and best practices can be used to develop high quality code to prevent web application attacks.
.Net is widely used by almost all organizations as the leading framework to build web applications. The course teaches developers how to identify security flaws and implement security countermeasures throughout the software development lifecycle to improve the overall quality of products and applications.
The course covers critical areas of .NET security such as Input Validation, Framework security, Authentication and Authorization, Session Management, Cryptography, Exception Handling, .NET Configuration, and Code Review. It also highlights the importance of Secure Development Life Cycle in developing robust and scalable applications.
The Fundamentals of .NET Application Security course lays the foundation required by all application developers and development organizations to produce applications with greater stability and fewer security risks to the consumer.
Secure Programming and Software Security
- What is Secure Programming?
- Software Security
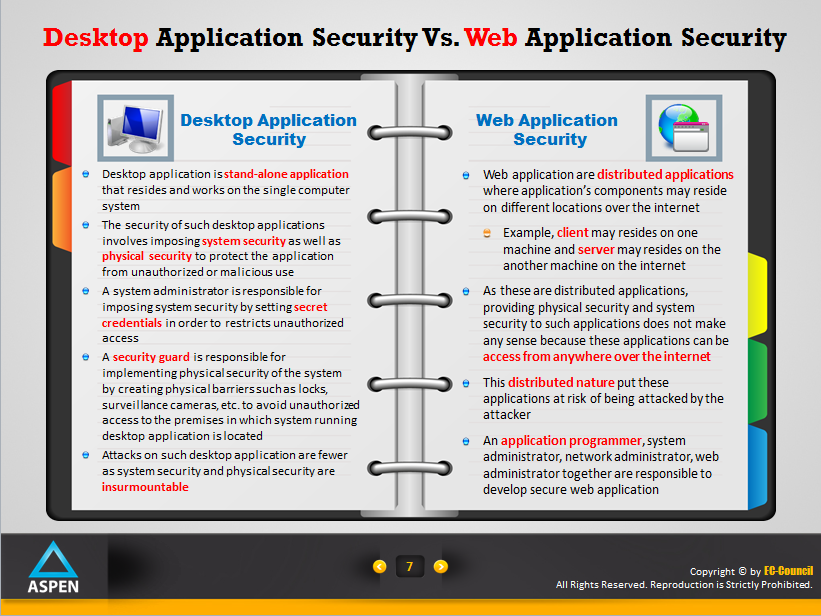
- Desktop Application Security Vs. Web Application Security
- Providing End-to-End Software Security
- Roles Involved in Providing End-to-End Software Security
- .NET Application Security
- Need for .NET Application Security
- Why are Security Mistakes Made?
- .NET Framework Security Namespaces
- Secure Coding Principles
Common Security Threats on .NET
- Common Security Threats on .NET
Securing .NET Input Validation
- Input Attacks Methodology
- Cross Site Scripting (XSS) Attacks
- SQL Injection Attacks
- Buffer Overflow Attacks
- Denial-of-Service (DoS) Attack
- Why Input Validation?
- Input Validation
- Input Validation Specification
- Input Validation Approaches
- Client-side Input Validation
- Server-side Input Validation
- Client-Server Input Validation Reliability
- ASP.NET Validation Controls
- Set of ASP.NET Validation Controls
- Advantages of ASP.NET Validation Controls
- Output Encoding
- ASP.NET Controls with Encoding Support
- Input Attacks Best Practices
.NET Framework security
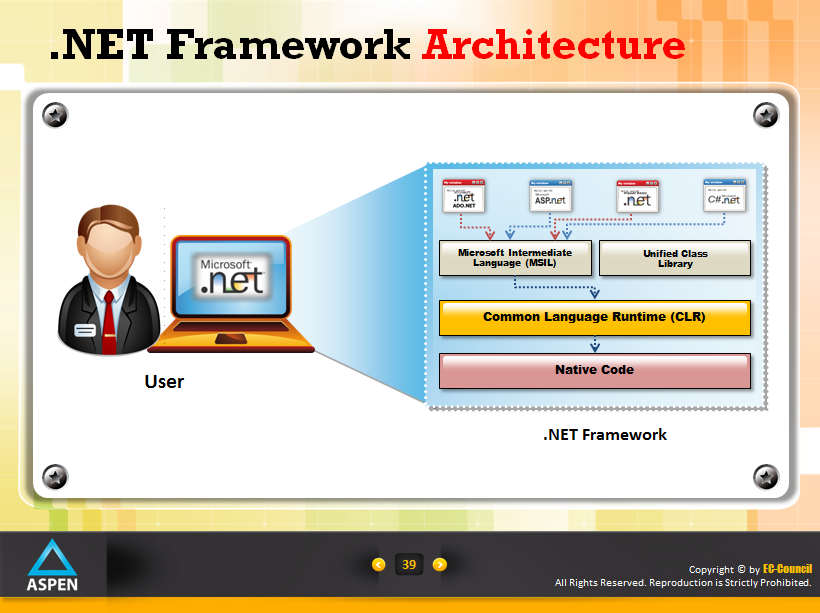
- .NET Framework Architecture
- How .NET Framework Helps Developer /Administrator to Build a Secure Application
- Basic Components of .NET Framework
- Key Elements of .NET Framework Architecture Security
- Best Practices for .NET Framework Security
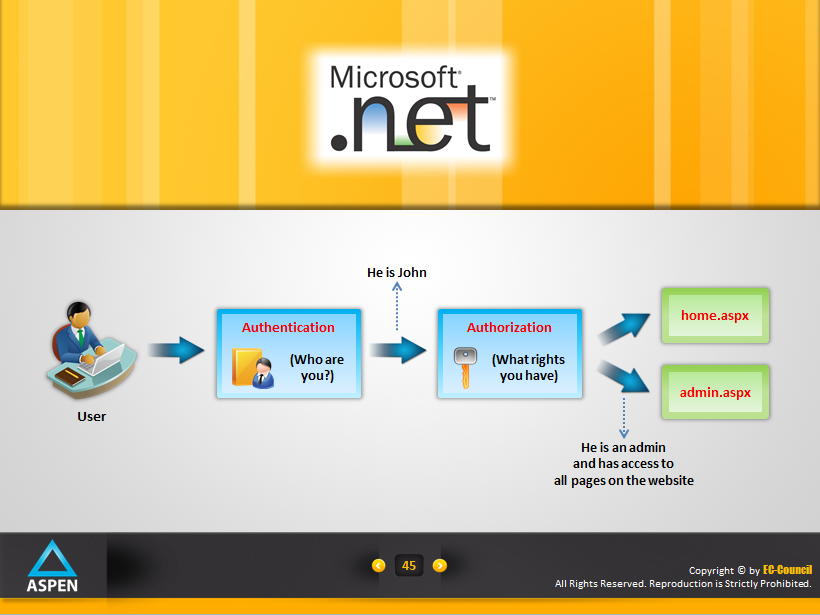
Securing .NET Authentication and Authorization
- Microsoft .NET
- Introduction
- Authentication and Authorization Threats
- ASP.NET Authentication
- ASP.NET Authentication Modes
- ASP.NET Authorization
- Identifying Authentication and Authorization Details
- Secure Development Checklists: Authentication
- Secure Development Checklists: Authorization
- Guidelines for Secure Authentication and Authorization Coding
Securing .NET Session Management
- Session Management
- Rules of thumb for Securing Session/Authentication Tokens
- Common Attacks on Sessions
- Recommendations to Prevent Session Hijacking Attack
- Recommendations to Prevent Token Prediction Attack and XSS Attack
- Recommendation to Prevent Session Replay Attack
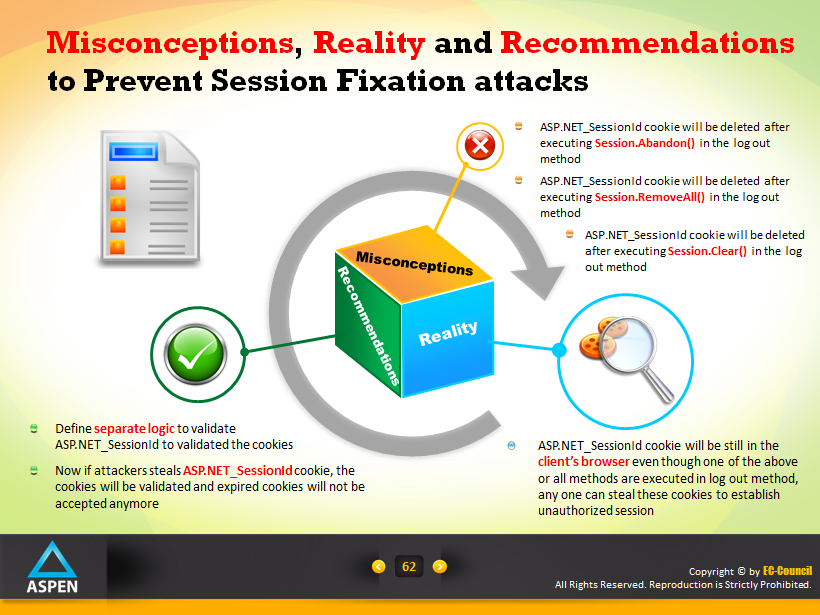
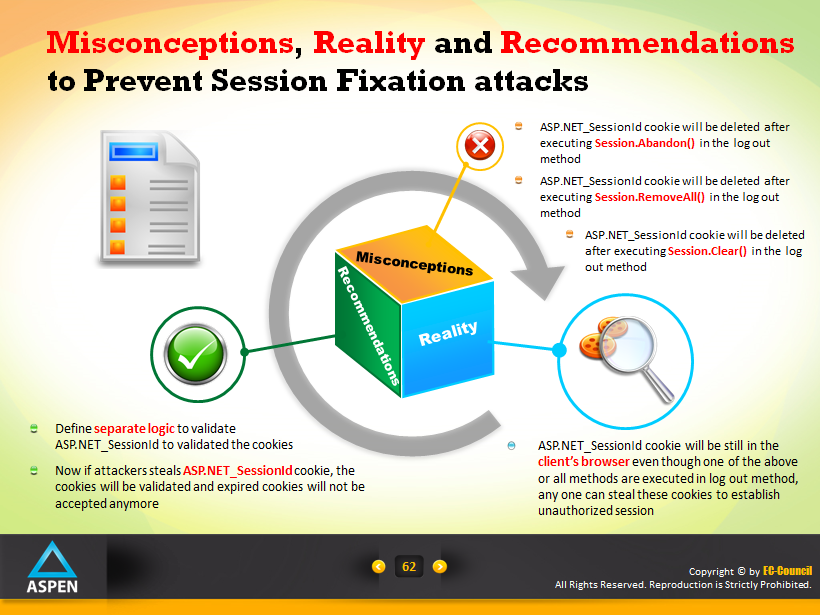
- Misconceptions, Reality and Recommendations to Prevent Session Fixation attacks
- Recommendation to Prevent Cross Site Request Forgery Attack
- General Guidelines for Secure Session Management
Securing .NET Cryptography
- What is Cryptography?
- Goals of Cryptography
- Common Threats on Cryptography and Their Mitigation Techniques
- Attacker’s Scenarios for Cryptography Attacks
- .NET Cryptography Namespaces
- Symmetric Encryption
- Securing Symmetric Encryption
- Asymmetric Encryption
- Securing Asymmetric Encryption
- Hashing
- Securing Hashing
- Digital Signatures
- Security Features of Digital Signatures
Securing .NET Exception Handling
- Parameters to be considered while Designing Secure Error Messages!
- Need of Error/Exception Handling
- Secure Exception Handling
- Handling Exceptions in an Application
- Best Practices for Coding Exceptions Safely
- Do’s and Don’ts in Exception Handling
- Guidelines for Proper Exception Handling
- Error Handling Security Checklists
Securing .NET Configuration
- Configuration Management
- What is Configuration Files?
- Why do Developers Need to Apply Secure Configuration Settings?
- ASP.NET Configuration Files Model
- Applying Secure Configuration Settings
.NET Secure Code Review
- Secure Code Review
- Why Secure Code Review?
- What should you Understand before Secure Code Review?
- Security Code Review Process
.NET Secure Development Lifecycle (SDL)
- What is SDL?
- Why SDL?
- Secure Development Lifecycle (SDL) Process
- Security in the Design Stage: Threat Modeling
- Guidelines for Applying Security in Implementation Phase of SDL
- Security Testing
Anyone interested in learning secure programming in .Net
Prerequisites:
Basic .Net Programming Knowledge
Duration:
4 Hours
 [break/]
[break/]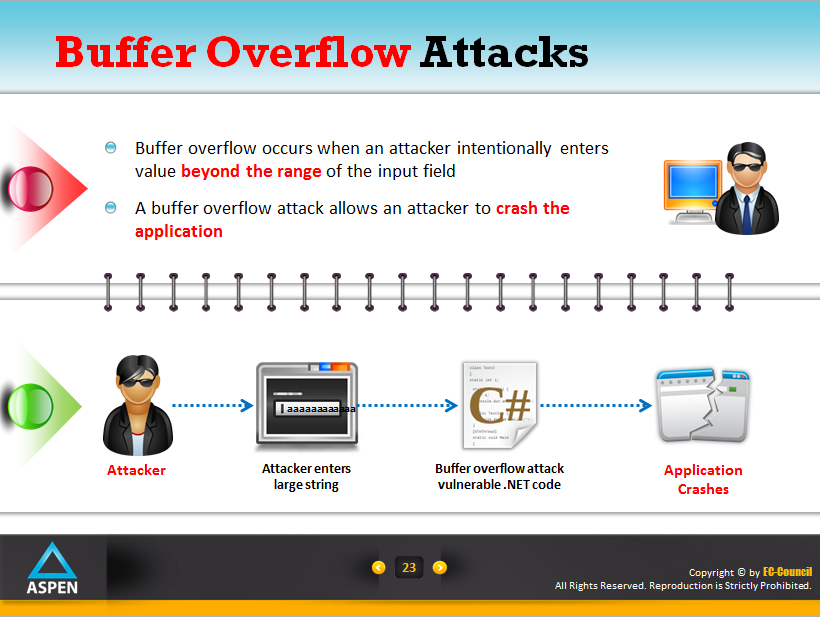
 [break/]
[break/]