Description
 [break/]
[break/]
 [break/]
[break/]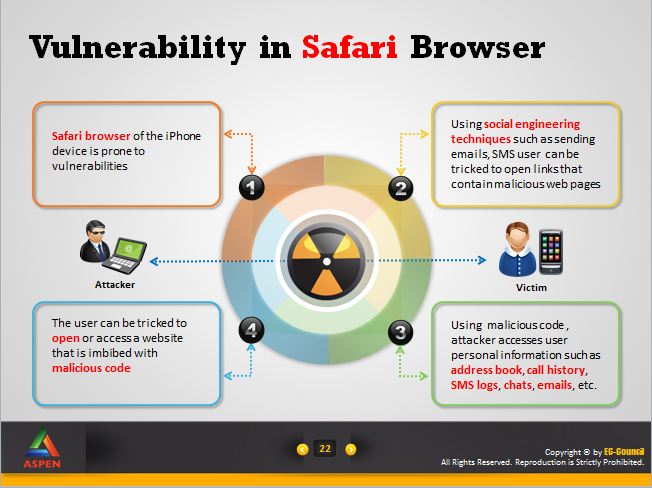
 [break/]
Smart phones have become the basic need for today’s mobile workforce. Smart phones are equipped with more powerful and enriched features when compared to the desktops. Modern smart phones provide us high resolution touch screens, web browsers to view standard webpages, Wi-Fi for data access etc. that makes a smart phone more widespread among users. iPhone, in the line of smartphones have reached the greater heights as they provide users with the most enhanced and elegant features. The apps for iPhone are made available to the users through the app store that is approved by Apple.
[break/]
Smart phones have become the basic need for today’s mobile workforce. Smart phones are equipped with more powerful and enriched features when compared to the desktops. Modern smart phones provide us high resolution touch screens, web browsers to view standard webpages, Wi-Fi for data access etc. that makes a smart phone more widespread among users. iPhone, in the line of smartphones have reached the greater heights as they provide users with the most enhanced and elegant features. The apps for iPhone are made available to the users through the app store that is approved by Apple.
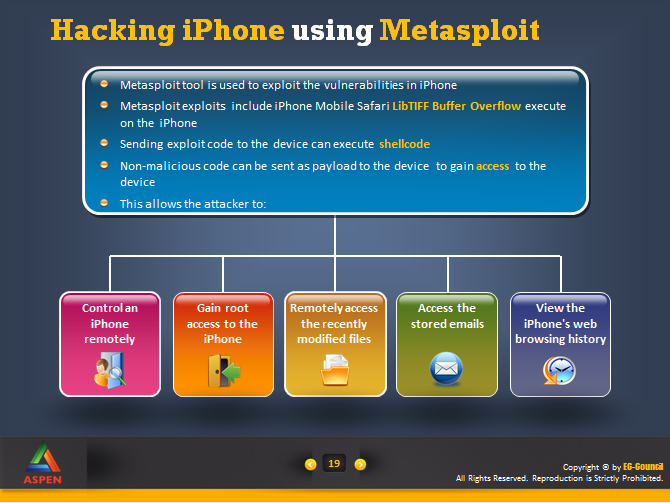
As usage increases, the security threat to the device also increases. The attackers use the most advanced techniques to gain complete access over the phone to extract user’s personal data along with monetary benefits.
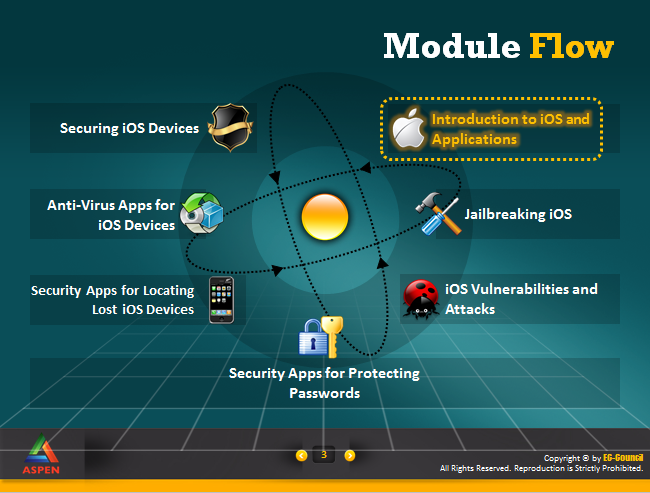
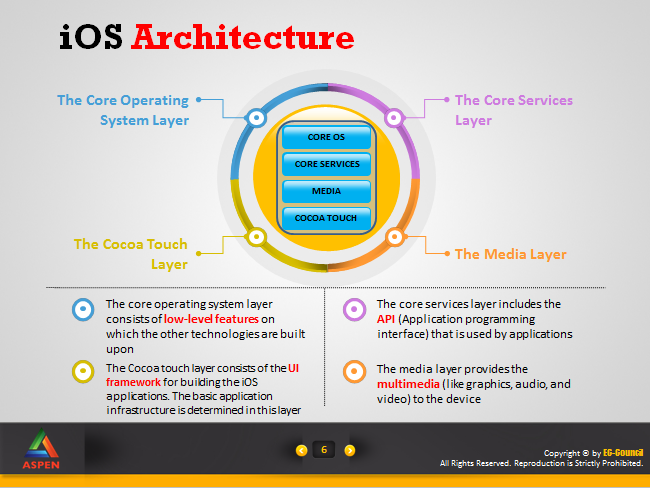
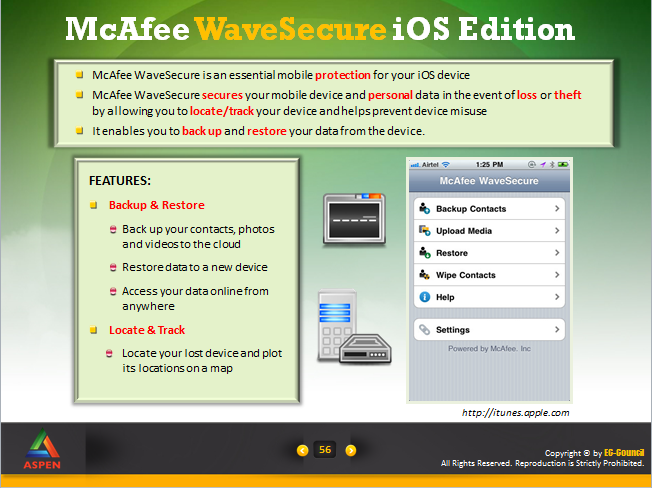
Securing iOS and apps course helps you to understand the existing threats and the best practices that need to be implemented in an efficient way to secure information. This course provides the students with sufficient knowledge about iOS operating system, its features and the architecture. It recommends the best practices that can be implemented to secure the iOS devices from various vulnerabilities. It also provides a list of security tools that are used to protect the iOS devices.
This course provides the necessary training that is required to the people who are interested in iOS security such as security engineers, security officers as well as vulnerability assessment professionals.
$1.00 – $1.00 Tax Incl.






